Fake LinkedIn Interview Used by Lazarus Hackers to Target AllSecure CEO
hackread.comResearchers at AllSecure have revealed how North Korean hackers from the Lazarus Group used a fake LinkedIn job interview and deepfake technology to target their CEO.
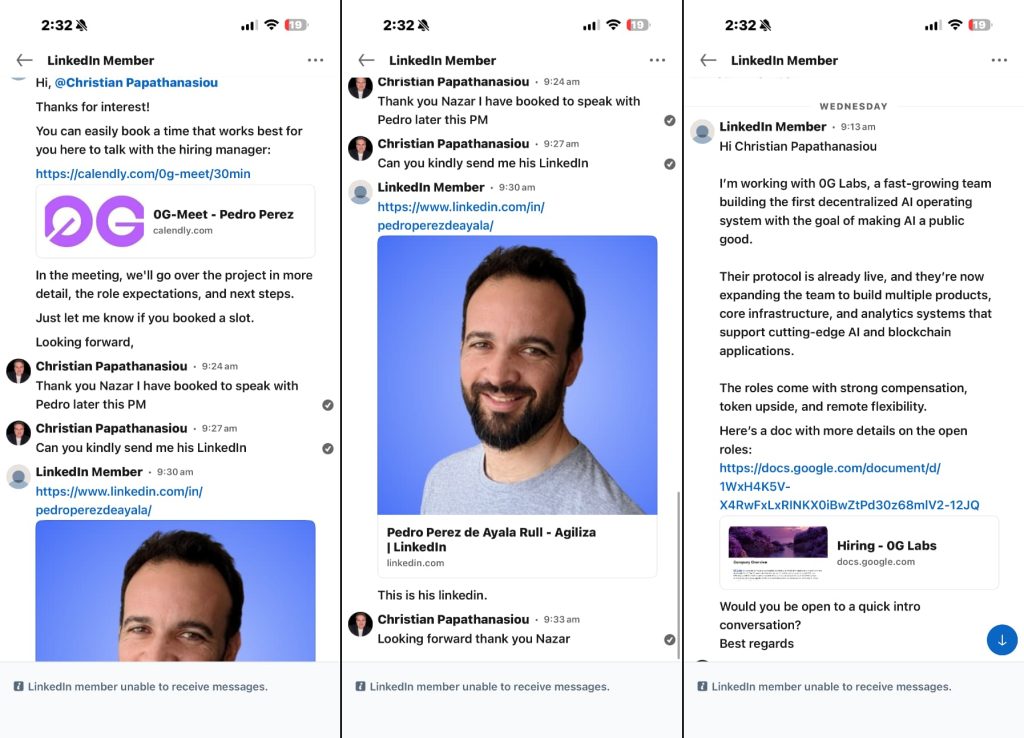
The notorious North Korean Lazarus Group has been caught trying to rob a CEO through a fake job interview. Just last week, the hackers used LinkedIn to target Chris Papathanasiou, the head of a security firm called AllSecure, in a state-sponsored malware campaign.
The approach was remarkably polished. A recruiter named Nazar reached out about a role at 0G Labs, a firm building an AI project. However, this wasn’t just a random message; it included a professional job description and a link to book a call with a hiring manager named Pedro Perez de Ayala. It is worth noting that the details of this incident and the subsequent research were shared with Hackread.com.
The Deepfake theory ...
Copyright of this story solely belongs to hackread.com . To see the full text click HERE