OpenClaw Vulnerability Allowed Websites to Hijack AI Agents
securityweekMalicious websites could open a WebSocket connection to localhost on the OpenClaw gateway port, brute force passwords, and take control of the agent.

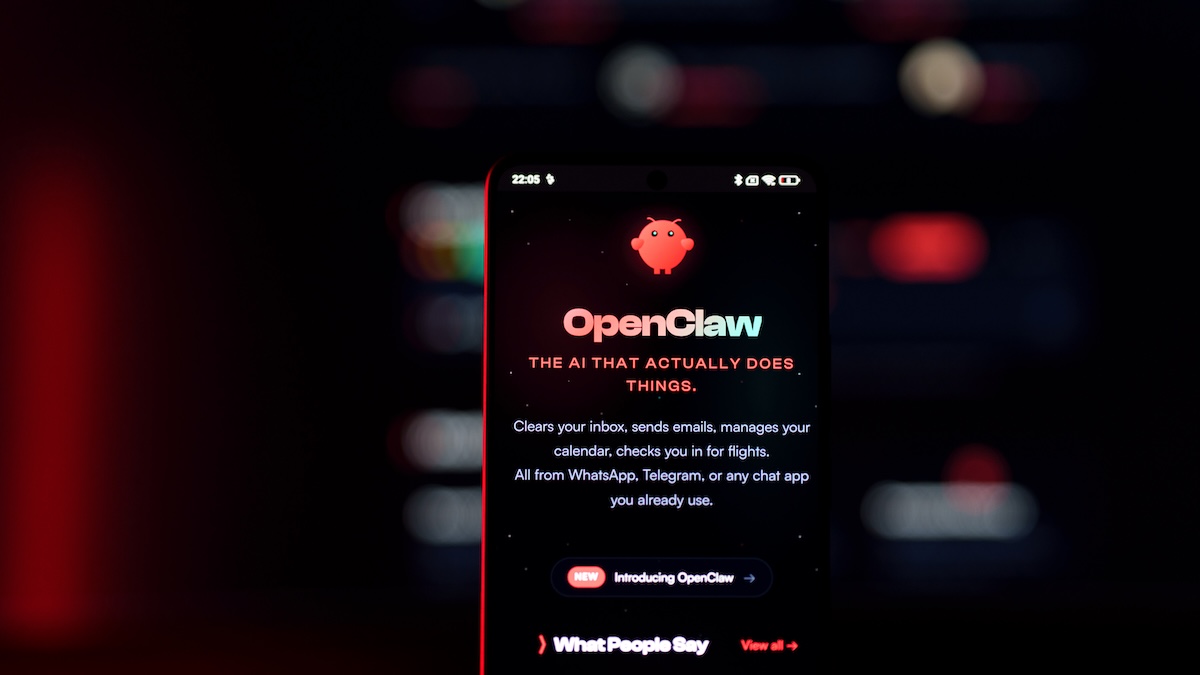
A vulnerability in the OpenClaw AI assistant could have allowed attackers to hijack agents by luring victims to malicious websites, Oasis Security reports.
Successful exploitation of the bug did not require the installation of malicious extensions or user interaction, instead relying on functionality within OpenClaw.
A self-hosted AI agent, OpenClaw runs a local WebSocket server, which acts as a gateway that handles authentication, orchestrates the agent, manages chat sessions, and stores configurations.
Applications and devices connect to the gateway as nodes to expose functionality, run commands, and access capabilities, while authentication is handled via tokens or passwords.
“The gateway binds to localhost by default, based on the assumption that local access is inherently trusted. That assumption is where things break down,” Oasis explains.
The cybersecurity firm discovered ...
Copyright of this story solely belongs to securityweek . To see the full text click HERE



